This sample Child Pornography Research Paper is published foreducational and informational purposes only. If you need help writing yourassignment, please use our research paper writing service and buy a paper on any topic ataffordable price. Also check our tips on how to write a research paper, see the lists of criminal justice research paper topics, and browse research paper examples.
The pictorial and written portrayal of children as sexual objects has existed through the millennia and across civilizations, with examples dating back to ancient Greece, Rome, China, and India (Bullough 2004; Linz and Imrich 2001). In the modern era, the nature and availability of child pornography has been driven by technological advances, first the invention of the camera in the early nineteenth century and more recently the advent of the Internet and associated digital technologies towards the end of the twentieth century. The Internet, in particular, has transformed the production, dissemination, and consumption of child pornography, increasing exponentially the amount of material available and the number of people accessing that material. Prior to the Internet, images were traded furtively in hard-copy form among relatively small groups of dedicated users. The technical quality of the images was poor, the range limited, and the distribution networks unreliable and highly restricted (Ferraro and Casey 2005). By the early 1980s, law enforcement agencies could justly claim considerable success in stemming the international and domestic trafficking of child pornography. With the Internet and digitization came the ability to access vast quantities of technically high-quality images, cheaply, apparently anonymously, and all from the comfort of home.
It is argued in this research paper that the current child pornography problem is the result of the interaction between two factors. First, child pornography would not exist if there was not a pool of individuals – mostly men – who derive sexual gratification from viewing sexual images of children. This pool comprises those who have a preferential sexual attraction to children, but it also includes many individuals with a latent, casual, or ill-formed potential to become aroused by sexual images of children. Second, the scale of the child pornography problem that confronts society in the twenty-first century is a function of the increased availability and ease of access of child pornography provided by the Internet. The Internet is not simply an alternative delivery mechanism by which dedicated offenders satisfy their sexual cravings, viewing material that they would have otherwise obtained through some other means; the Internet has played an active role in stimulating the growth of child pornography, drawing in many individuals who, in the pre-Internet era, would have had neither the necessary drive nor the know-how to seek out and obtain child pornography.
What Is Child Pornography?
Child pornography is defined as a legal term for the purposes of investigation and prosecution and as a working construct for the purposes of research, prevention, and advocacy. A problem with legal definitions is that the meaning of both “child” and “pornography” varies from jurisdiction to jurisdiction. The age of consent around the world can be as low as 12 years (e.g., some parts of Mexico) and as high as 18 years (some jurisdictions in the United States), with 16 years perhaps the most common in the Western world (e.g., the United Kingdom, the Netherlands, New Zealand, Canada, and most parts of Australia) (e.g., Avert n.d.). Likewise, definitions of pornography also vary, and acts that are illegal in some countries may be legal in others. Generally, however, legal definitions distinguish between obscene material and artistic portrayals of nudity and eroticism, judging what is acceptable or unacceptable against community standards. Typically, more stringent standards are applied to images involving children than to images involving adults; child pornography need not necessarily involve obscene behavior but may include acts that are lascivious or suggestive.
The International Centre for Missing and Exploited Children (2008) conducted an audit of child pornography legislation among the 187 members of Interpol. It found that 36 countries do not specifically criminalize possession of child pornography, while a further 95 countries had no child pornography legislation at all. For countries that do define child pornography, there are variations in the exact content of the legislation. Apart from the age of the child, there is disagreement about whether computer-generated images are legal. For example, in a recent Australian case, a cartoon depicting Bart and Lisa from the Simpsons engaged in sexual acts was found to be pornographic, a judgment that could not occur in the USA.
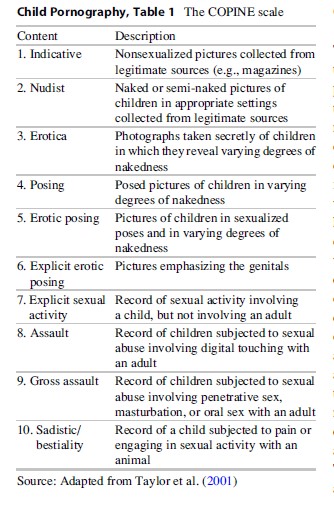
Nonlegal definitions of child pornography can be more broadly framed than legal definitions and so avoid some of the debates around specific elements. According to the Office of the United Nations High Commissioner for Human Rights (2002), “Child pornography means any representation, by whatever means, of a child engaged in real or simulated explicit sexual activities or any representation of the sexual parts of a child for primarily sexual purposes.” Child pornography may include still photographs, videos, audio recordings, and written material. It also may involve a wide range of acts that vary in degree of explicitness. Taylor et al. (2001) developed the COPINE scale that delineated ten levels of child pornography severity, ranging from nonsexualized pictures of children collected from legitimate sources such as magazines to graphic depictions of children engaging in sexual acts with other children, adults, and even animals (Table 1). In a content analysis of child pornography identified by the Internet Watch Foundation (2010), 73 % of victims were assessed as being under 10 years of age, and around two-thirds of the images involved penetrative sexual activity between the victim and an adult, equivalent to levels nine to ten on the COPINE scale.
It should be noted that many researchers and advocacy groups object to the term child pornography, believing that it trivializes the severity of the behavior and may facilitate excuse-making by offenders by linking it to consensual adult erotica. It is argued that every so-called child pornography image is a record of a child’s sexual exploitation. Alternative terms include child abuse images, child sexual abuse material, documented child sexual abuse, and child exploitation material.
Child Pornography And The Internet
The Internet and associated technologies have transformed the way that child pornography is produced, how it is distributed to users, and how those users view and retain it. While child pornography may be produced professionally by organized crime groups, the ready availability of inexpensive electronic recording devices (digital cameras and video recorders) permits individual offenders to create “high-quality,” homemade images involving records of their own sexual abuse exploits. The Internet then pro-vides an unparalleled distribution network, connecting producers and users from all corners of the world. As with the production phase, the distribution of child pornography may involve organized crime rings, but the Internet also allows offenders to interact directly with one another, exchanging files and providing information and social support. For users, the Internet means that vast quantities of child pornography can be acquired inexpensively and accessed with apparent anonymity at any time or place. The downloaded images do not deteriorate and can be conveniently catalogued, stored, and retrieved.
The Internet provides a number of methods by which child pornography can be distributed and accessed. Child pornography websites may be posted on the World Wide Web. Around three-quarters of these child pornography websites are commercial enterprises (Internet Watch Foundation 2008). In order to thwart detection efforts of authorities, images are often hosted on temporary websites, and customers may need to negotiate numerous redirects before they arrive at the target site. If a particular website is closed down, the images may reappear shortly thereafter at another location. Nevertheless, the open web is a relatively risky place to seek child pornography and tends to attract novice offenders; through the vigilance of the police and Internet service providers, the more dedicated and experienced offenders are increasingly being driven to deeper levels of the Internet (Jenkins 2001). Offenders may communicate directly with one another via chat rooms, newsgroups, bulletin boards, and peer-to-peer networks (Ferraro and Casey 2005; Wortley and Smallbone 2006, 2012). Entry into these offender networks may be highly controlled; potential members may need to gain the trust of existing members, and a password may be required to order to participate. As discussed further on, infiltration of these groups by undercover police is a major priority of agencies tasked with controlling child pornography.
Estimates of the size of the Internet child pornography problem are notoriously rubbery, usually involving little more than someone’s best guess. Various indices have been used. The number of offenders worldwide has been estimated in the millions (National Center for Missing and Exploited Children 2005); the number of children estimated to be victims of child pornography is between 10,000 and 100,000 (Maalla 2009); at any one time, there are estimated to be over one million pornographic images of children on the Internet, with 200 new images posted daily (Wellard 2001); offenders have been arrested with as many as a million downloaded child pornography images (NewsFlavor 2011); and child pornography on the Internet is estimated to turn over between $3 billion (Ropelato 2003) and $20 billion (Hoover 2006) per year. Some have cautioned against the uncritical acceptance of such figures and being swept along in a moral panic (Jewkes 2010; Schottenfield 2007). Nevertheless, most commentators agree that child pornography is a serious problem that has escalated dramatically with the growth of the Internet.
Who Are The Offenders?
Perhaps the most remarkable feature of identified child pornography offenders is their general lack of remarkable features. There is no single offender type and nor is there a consistent set of sociodemographic or psychological characteristics that distinguish offenders from nonoffenders. Those arrested for downloading online child pornography have come from all walks of life and have included judges, dentists, soldiers, teachers, rock stars, and police officers. In a survey of 605 individuals arrested for possession of child pornography in 2006, Wolak et al. (2011) found that most were white (89 %), male (99 %), 26 years of age or older (89 %), and in full-time employment (61 %). Thirty-one percent were married or living with a partner, 29 % earned more than $50,000 per year, and 16 % were college graduates. A minority had previous sexual (9 %) or nonsexual (27 %) offence convictions.
Psychological assessments of offenders have produced mixed and sometimes conflicting findings, with few clearly distinguishing features emerging. Few arrestees have been found to be mentally ill (6 %) or sexually disordered (5%) (Wolak et al. 2011). Laulik et al. (2007), using the Personality Assessment Inventory, found that fewer than 10 % of offenders scored in the clinically significant range on any of the clinical scales, with the exception of depression (30 %), borderline features (17 %), and schizophrenia (13 %). Tomak et al. (2009) compared child pornography offenders with incarcerated contact sexual offenders on the Minnesota Multiphasic Personality Inventory. Mean scores fell below the clinically significant levels for both groups, with the child pornography offenders scoring significantly lower than the other group on the psychopathic deviation and schizophrenia scales. Babchishin et al. (2011) conducted a metaanalysis of studies that have used psychological inventories to compare child pornography offenders with other sex offenders. In general, online offenders had fewer problems with victim empathy, cognitive distortions, and emotional identification with children, and there were no differences in loneliness and self-esteem. However, online offenders showed greater sexual arousal to images of children than did contact offenders, suggesting higher levels of pedophilia. One explanation for this latter finding is that the laboratory conditions under which sexual arousal was measured closely resemble the actual behavior of online offenders. In other words, sexual arousal on online offenders may be specifically triggered by sexual images of children, but this may not necessarily indicate a generalized sexual attraction to children in an offline environment (Wortley and Smallbone 2012).
It should be noted that almost all studies examining the characteristics of child pornography offenders have involved incarcerated samples. This is problematic because police tend to target the most serious offenders for investigation, and so results of research on these offenders are likely to be skewed. In a rare exception, Seigfried et al. (2008) anonymously surveyed 307 general Internet users. They found that 30 respondents admitted to having accessed child pornography online. Most surprisingly, ten of the users were females, representing a rate of offending that far exceeds official arrest figures. Overall 16 % of males and 6 % of females admitted accessing child pornography. There were no differences between users and nonusers on the “big-five” personality dimensions (extraversion, neuroticism, openness, conscientiousness, and agreeableness), but users scored lower on internal moral choice and higher on amoral dishonesty, suggesting that they were more likely to construe their behavior as morally acceptable. Overall, these findings indicate that there is a significant “dark figure” of child pornography use and that differences between offenders and non-offenders shrink when the full range of offenders is taken into consideration.
Perhaps the most contentious issue concerning the characteristics of offenders is the extent to which users of child pornography also engage in contact sexual offending. Conceptually the relationship between online and contact offending may take several forms. Child pornography may be sought out by individuals who have an existing sexual attraction to children; child pornography may have a long-term corrosive effect, and individuals may become increasingly attracted to child pornography and desensitized to the harm experienced by victims; or child pornography may be the sole outlet for an individual’s sexual attraction to children and may even help him resist engaging in contact offending (Wortley and Smallbone 2006). In a meta-analytic review of the research, (Seto et al. 2011) found that on average 12 % of child pornography offenders also had official contact sexual offending histories, with the range reported in individual studies between 0 % and 43 %. Examining self-report data, the average prevalence of contact offending was 55 % with a range of 32–85 %. However, the studies examined by Seto et al. did not distinguish between child pornography users and child pornography producers. A great deal of the available child pornography involves offenders recording their own sexual abuse exploits and so necessarily involves contact offending. Again, too, all of the research in this area has been conducted on convicted offenders who, because of the priorities set by police when selecting cases to investigate, may be more likely than undetected offenders to also commit contact offences. It remains unclear how many individuals who view child pornography also commit contact offences.
While the research reviewed in this section generally indicates that on average child pornography offenders exhibit few distinguishing sociodemographic or psychological, some studies have reported considerable within group variation. It may be that averaged findings mask the existence of distinct subtypes of offenders. Cooper et al. (1999) suggested a three-category typology of general Internet pornography users that may be useful when considering the particular case of child pornography users. The categories are:
1. Recreational users: They access pornography sites on impulse, out of curiosity, or for short-term entertainment. They are not seen to have long-term problems associated with pornography use.
2. At-risk users: They are vulnerable individuals who have developed an interest in pornography, but may not have done so had it not been for the Internet.
3. Sexual compulsive: They seek out pornography to satisfy existing pathological sexual interests.
This typology, while not yet empirically verified for child pornography offenders, has good face validity and can help explain the dramatic escalation in the child pornography problem that has accompanied the growth of the Internet. While it may be comforting to divide the world neatly into pedophiles (“them”) and nonpedophiles (“us”), in reality the potential to become sexually attracted to children falls along a continuum, and under the “right” conditions many men may be tempted to view child pornography (Wortley and Smallbone 2012). For the individuals in categories 1 and 2 of Cooper et al.’s (1999) typology, the Internet has provided the easy opportunity for them to explore hidden thoughts and desires in order to satisfy their sexual curiosities. Moreover, the virtual world is a disinhibiting environment that encourages individuals to engage in riskier behavior than they would ever consider in the real world (Quayle and Taylor 2001). Had these individuals lived in the pre-Internet era, it is likely that most would not have gone to the effort to seek out hard-copy child pornography. To be sure, there are offenders (those in category 3 of the typology) who are unambiguously attracted to children and who will determinedly and repeatedly seek out opportunities to access child pornography. Even for these offenders, however, had they lived in the pre-Internet era, the task of locating child pornography would have been much more difficult, their choice would have been restricted, and their collection of images would have been much smaller.
Policing The Net
The investigation of child pornography on the Internet presents unique challenges for law enforcement agencies (Wortley and Smallbone 2012). The Internet is complex network of networks with a decentralized structure that makes it difficult to screen content, enforce legislation, and track offenders. Even if one pathway to a child pornography site is blocked, there are many alternative pathways that can be taken to reach the same destination. Moreover, the reach of the Internet is global, and local citizens may access child pornography images that were produced and stored on another continent. Most investigations of child pornography on the Internet, therefore, will cross jurisdictional boundaries and require cooperation among agencies, often at an international level. International cooperation is in turn impeded by a lack of effective legislation in many countries and inconsistencies between countries where legislation does exit
(International Centre for Missing and Exploited Children 2008). There is variation, too, in the capacity and commitment of countries to enforce child pornography laws and to act against offenders, either because of cultural reasons, through a lack of resources and know-how, or because of corruption (UNICEF 2009). In addition, rapid technological developments such as peer-to-peer networks, anonymous remailers, and file encryption make it easier for offenders to avoid detection (Ferraro and Casey 2005). Finally, the sheer volume of child pornography on the Internet and the number of offenders accessing that pornography can simply overload police resources. Police cannot hope to arrest every offender of whom they become aware and must prioritizetheir effort, for example, by targeting those offenders who possess “firstgeneration” (i.e., previously unknown) images that indicate the offender has made a record of his own sexual offending.
In order to meet these challenges, police must acquire new knowledge about the characteristics and modus operandi of child pornography offenders, develop specialized technical expertise in online offending, and forge links with other police agencies, the Internet industry, and nongovernment organizations. Many larger police departments will have dedicated Internet child exploitation teams. These teams may be supported by national agencies that provide specialized expertise and training, maintain centralized databases, track offenders and victims across jurisdictions, and help coordinate investigations. The activities of national agencies may in turn be coordinated through various international agencies and programs. An example is the Virtual Global Taskforce (VGT), an international partnership comprising nine members – national agencies from seven counties (Australia, Canada, Italy, New Zealand, the United Arab Emirates, the United Kingdom, and the United States) and two international agencies (Europol and Interpol). The VGT conducts coordinated international law enforcement operations and helps track down victims and offenders across borders.
Krone (2005) suggests that police investigations can be divided into four main types. The first type of investigation involves the targeting of individual offenders. Investigations may begin with information received from the public, for example, via one of the various child pornography hotlines. Child pornography may also be discovered during the investigation of contact child sexual abuse cases. There are also a number of documented cases in which computer repairers have found child pornography on an offender’s hard drive and notified police. The most notorious case this category involved the pop singer Gary Glitter.
The second type of operation targets offenders who are members of covert groups and who operate in closed chat rooms, newsgroups, and peer-to-peer networks. Investigation may require police to operate undercover, infiltrating an offender group in the guise of a prospective member. Once the group has been infiltrated, the arrest of one offender and the interrogation of his Internet records can quickly lead to the arrest of other members of the group. There have been a number of international operations targeting covert groups, including Operation Cathedral, Operation Ore, and Operation Rescue (Wortley and Smallbone 2012). Operation Rescue, for example, involved the investigation of a covert newsgroup that was run from the Netherlands and had 70,000 members across the United Kingdom, the United States, New Zealand, Australia, and Thailand. The group was detected in 2007 by investigators in Australia and the United Kingdom, and an operation was launched, coordinated through the VGT. Officers infiltrated the group and took over the account of the UK administrator, giving them access to the member list. The Dutch founder of the group was jailed and 640 members were identified, 184 of whom were arrested.
The third type of operation targets website subscribers. These are offenders who purchase access to child pornography sites, which are typically set up as commercial enterprises. Because offenders need to pay for images, once accounts of the business are seized, offenders are usually tracked through their credit card details. The operation targeting Landslide Productions (called Operation Avalanche in the United States and Operation Ore in the United Kingdom) is perhaps the best known in this category. Landslide Productions was a child pornography company run by from Ft Worth in Texas and involved a complex network of some 5,700 computer sites around the world. Online customers, of whom there were more than 250,000, provided credit card details to obtain network access. The investigation began in 1999 when the US Postal Inspection Service discovered that Landslide’s customers were paying monthly subscription fees into a post office box or via the Internet. A joint investigation between the Postal Inspection Service and the Internet Crimes Against Children Task Force (ICAC) was conducted over 2 years. Landslide’s accounts were seized and officers tracked down the owners of credit cards used to pay for site access. There were 120 arrests in the United States, including the ringleaders in Texas and 1,300 arrests in the United Kingdom.
The fourth type of operation involves police stings. Stings may take a number of different forms. Undercover police may enter youth-oriented chat rooms posing as children and engage predatory pedophiles lurking in the group. Police may also set up “honeypot” traps, the best known example of which was Operation Pin. The operation was started in 2003 by West Midlands (UK) police and expanded to include other VGT members (the FBI, the Australian Federal Police, the Royal Canadian Mounties, and Interpol). A bogus website was set up purporting to contain child pornography. Visitors to the site were required to go through a series of web pages and at each point it was reinforced that they were in a child pornography site. If they ultimately tried to access an image, their credit card details, which they were required to provide to log in, were captured. The operation has resulted in numerous arrests although precise numbers are not available.
Prevention
Despite the best efforts of police, arresting offenders is not a viable long-term solution to the problem of Internet child pornography. Certainly, offenders – and especially those involved in the direct sexual abuse of children – ought to be targeted by law enforcement personnel and arrested where possible. But no more than a few thousand people are arrested annually for child pornography offences in the United States (Wolak et al. 2011) and fewer still in other countries. As has been discussed, even highly successful coordinated international operations typically result in fewer than a couple of hundred arrests worldwide. If we accept that the number of individuals actively accessing child pornography via the Internet is in the millions, these figures represent a drop the bucket. For similar reasons, we cannot rely on the therapeutic interventions with known offenders – the usual response of psychologists – to make any significant dent in the problem. The prevention of Internet child pornography cannot be approached simply as a problem of individual sexual deviancy. The proliferation of child pornography in the Internet age has been a function of the increased opportunity offenders have been given to access images, and tackling the child pornography problem in any serious way must be centered on reducing that opportunity.
The task of reducing the opportunities offered by the Internet can be viewed in terms of the situational crime prevention model (Clarke 2008). This involves increasing the effort, increasing the risks, reducing rewards, removing excuses, and reducing provocations associated with accessing child pornography. The following discussion provides an example of each of these strategies. The list is not intended to be exhaustive (see Wortley and Smallbone 2012, for a more detailed analysis).
Increasing the effort involves making it more difficult for offenders to access images on the Internet. The principal strategy is to reduce the amount of child pornography that is available. When police become aware of child pornography on the Internet in many jurisdictions, they are empowered to issue a notice and take down (NTD) order, requiring Internet service providers (ISPs) to remove or filter (i.e., block the pathway to) the offending images. Arguably there has been some success in reducing the volume of child pornography in open areas of the Internet such as the World Wide Web. The Internet Watch Foundation (2010) reported that they took action against nearly 17,000 child pornography domains in 2010 and that it has on average 500 domains on its blacklist at any one time. One consequence of police activity has been to drive offenders to deeper and more secure levels of the Internet. While this is of concern, it is evident that offenders feel vulnerable in open areas of the Internet. The more hidden child pornography becomes, the more difficult it is for the offenders themselves to access it.
Increasing the risks most obviously involves making it more likely that the offender’s online behavior will be detected. As has been discussed, however, even with active policing of the Internet realistically, an individual’s chance of being arrested is in fact very small. But the risk of detection and the perceived risk of detection are two different things. Police stings described earlier demonstrate the importance of this distinction. It is noteworthy that the launch of Operation Pin was accompanied by widespread media coverage. The police did not hide fact that they were setting up honeypot traps, but rather they gave offenders explicit forewarning. Their aim was not to maximize the number of arrests but to create the uncertainty in the mind of potential offenders about safety of sites that they were considering accessing.
Reducing rewards involves frustrating attempts by offenders to derive benefits from child pornography. This strategy has been used particularly to target the distributers of child pornography who are seeking to benefit themselves financially. The Financial Coalition Against Child Pornography (FCACP) is a grouping of 35 ISPs, credit card companies, banks, and other companies providing online payment services. The goal of FCACP is to undermine the commercial viability of child pornography by tracking the flow of money in child pornography transactions and blocking payments for illegal downloads. The Financial Coalition Against Child Pornography (2011) claim that there has been a 50 % drop in the number of commercial child pornography sites following their activities. There has also been a dramatic increase in the cost of commercial child pornography as a result of the financial squeeze that has been applied, with monthly subscriptions rising from around $30 per month in 2006 to as much as $1,200 per month.
Removing excuses involves permitting offenders fewer opportunities to minimize the seriousness of child pornography offending. Offenders may take comfort in the belief that viewing child pornography does no harm (e.g., “They are just images not real people”) and even that it is not illegal. Some countries (e.g., Norway) include an additional element in the NTD procedures designed to challenge these excuses. When access to a child pornography site is blocked, instead of a standard error message, the person trying to access the site receives a “stop” page containing a warning message. The precise wording of the stop page can vary, but the general intention is to make it clear to the potential offender that the behavior he is contemplating is illegal.
Reducing provocations involves removing situational factors that might trigger the impulse to view child pornography. For many offenders involvement with child pornography is an insidious, progressive process (Quayle and Taylor 2003). One pathway to child pornography is through legal adult-focused pornography and child pornography embedded within legal sites may be particularly problematic. Individuals may first encounter child pornography without having to actively seek it out and when they are already sexually aroused. While law enforcement agencies rightly focus resources on the most serious forms of child pornography, which typically appears on dedicated sites, attention should also be given to embedded child pornography.
Conclusion
While child pornography has a long history, the scale of the problem has increased exponentially since the introduction and rapid growth of the Internet. There are undoubtedly many more child pornography images available now, and many more individuals accessing those images, than would have been the case images had the Internet not existed. The Internet has created opportunities for individuals with no more than a casual interest in child pornography to satisfy their sexual curiosities and has allowed dedicated offenders to give full expression to their obsession, amassing collections that may exceed a million images. The Internet is not just an alternative method by which child pornography may be accessed; the Internet is a cause of child pornography.
Policing the Internet presents unique challenges for law enforcement. Despite the establishment of dedicated police units to tackle child pornography, and unprecedented international cooperation, the sheer volume of the problem threatens to overwhelm policing resources. Capturing personal details of offenders and launching prosecutions against those individuals is time consuming and resource intensive, and police become aware of many more offenders than they could possibly arrest. As well as prioritizing efforts on the most serious offenders, greater attention must be given to prevention. If the current child pornography problem is a product of the increased opportunities afforded by Internet, then solutions to the child pornography problem must seek to reduce these opportunities. Admittedly the task is not an easy one and it is easy to become pessimistic about the chances of success. But it is undoubtedly true that without the current prevention efforts, the problem would be much worse than it currently is.
Bibliography:
- Avert (n.d.) Worldwide ages of consent. Available at http://www.avert.org/age-of-consent.htm
- Babchishin KM, Hanson RK, Hermann CA (2011) The characteristics of online sex offenders: a meta-analysis. Sex Abuse: J Res Treat 23(1):92–123
- Bullough VL (2004) Children and adolescents as sexual beings: a historical overview. Child Adolesc Psychiatr Clin North Am 13:447–459
- Clarke RV (2008) Situational crime prevention. In: Wortley R, Mazerolle L (eds) Environmental criminology and crime analyses. Willan, Cullompton, pp 178–194
- Cooper A, Putnam DE, Planchon LA, Boies SC (1999) Online sexual compulsivity: getting tangled in the net. Sex Addict Compuls 6(2):79–104
- Ferraro MM, Casey E (2005) Investigating child exploitation and pornography: the internet, the law and forensic science. Elsevier Academic Press, London
- Financial Coalition Against Child Pornography (2011) Report on trends in online crime and their potential implications in the fight against commercial child pornography. Available at http://www.missingkids.com/ missingkids/servlet/PageServlet?LanguageCountry¼en_ US&PageId¼3703
- Hoover JN (2006) As child porn industry grows, coalition launches counterattack. Information Week. 17 March. Available at http://www.informationweek.com/news/183700580
- International Centre for Missing & Exploited Children (2008) Child pornography: model legislation & global review, 5th edn. Available at http://www.icmec.org/ missingkids/servlet/PageServlet?LanguageCountry¼en_X1&PageId¼4348
- Internet Watch Foundation (2008) Annual and charity report. http://www.iwf.org.uk/accountability/annualreports/2008-annual-report
- Internet Watch Foundation (2010) Annual and charity report. Available at http://www.iwf.org.uk/accountability/annual-reports/2010-annual-report
- Jenkins P (2001) Beyond tolerance: child pornography on the internet. New York University Press, New York
- Jewkes Y (2010) Much Ado about nothing? Representations and realities of online soliciting of children. J Sex Aggress 16(1):5–18
- Krone T (2005) International police operations against online child pornography. Trends & issues in crime and criminal justice, No. 296. Canberra, Australia: Australian Institute of Criminology. Available at http://www.aic.gov.au/documents/3/C/E/%7B3CED11B0-F3F4-479C-B417-4669506B3886%7Dtandi296.pdf. Accessed 29 Apr 2010
- Laulik S, Allam J, Sheridan L (2007) An investigation into maladaptive personality functioning in internet sex offenders. Psychol Crime Law 13:523–533
- Linz D, Imrich D (2001) Child pornography. In: White SO (ed) Handbook of youth and justice. Kluwer Academic/Plenum, New York, pp 79–114
- Maalla NM (2009) Promotion and protection of all human rights, civil, political, economic, social and cultural rights, including the right to development. Report of the Special Rapporteur on the sale of children, child prostitution and child pornography. United Nations, General Assembly, Human Rights Council
- National Center for Missing and Exploited Children (2005) Child porn among fastest growing internet businesses. Available at http://www.missingkids.com/missingkids/servlet/NewsEventServlet?LanguageCountry¼en_US&PageId¼2064
- NewsFlavor (2011) British man in possession of the largest collection of child pornography in history. NewsFlavor, 16 July. Available at http://newsflavor.com/alternative/british-man-in-possession-of-the-largest-collection-of-child-pornography-in-history/#ixzz1ZRvZUZ6k
- Office of the United Nations High Commissioner for Human Rights (2002) Optional protocol to the convention on the rights of the child on the sale of children, child prostitution and child pornography, G.A. Res. 54/263, Annex II, U.N. Doc. A/54/49, Vol. III, art. 2, para. c, entered into force 18 Jan 2002. Available at http://www2.ohchr.org/english/law/crcsale.htm
- Quayle E, Taylor M (2001) Child seduction and self-representation on the internet. Cyberpsychol Behav 4:597–608
- Quayle E, Taylor M (2003) Model of problematic internet use in people with a sexual interest in children. Cyberpsychol Behav 6(1):93–106
- Ropelato J (2003) Pornography statistics 2003. Available at http://web.archive.org/web/20030621095030/ http://www.internetfilterreview.com/internet-pornography-statistics.html
- Schotenfield DL (2007) Witches and communists and internet sex offenders, oh my: why it is time to call off the hunt. St Thomas Law Rev 20:359–386
- Seigfried KC, Lovely RW, Rogers MK (2008) Selfreported online child pornography behavior: a psychological analysis. Int J Cyber Criminol 2(1):286–297
- Seto MC, Hanson RK, Babchishin KM (2011) Contact sexual offending by men with online sexual offenses. Sex Abuse: J Res Treat 23(1):124–145
- Taylor M, Quayle E, Holland G (2001) Child pornography, the internet and offending. Can J Policy Res (ISUMA) 2(2):94–100
- Tomak S, Weschler FS, Marjan G-H, Thomas V, Nademin ME (2009) An empirical study of the personality characteristics of internet sex offenders. J Sex Aggress 15:139–148
- UNICEF (2009) Handbook on the optional protocol on the sale of children, child prostitution and child pornography. UNICEF Innocenti Research Centre, Florence
- Wellard S (2001) Cause and effect. Community Care 1364:26–27, 15th–21st March
- Wolak J, Finkelhor D, Mitchell KJ (2011) Child pornography possessors: trends in offender and case characteristics. Sex Abuse: J Res Treat 23(1):22–42
- Wortley R, Smallbone S (2006) Child pornography on the internet. Problem-oriented guides for police. problemspecific guides series No. 41. U.S. Department of Justice. Available at http://www.popcenter.org/problems/ child_pornography/
- Wortley R, Smallbone S (2012) Internet child pornography: causes, investigation and prevention. Praeger, Santa Barbara
See also:
Free research papers are not written to satisfy your specific instructions. You can use our professional writing services to buy a custom research paper on any topic and get your high quality paper at affordable price.